Engineering & Transportation
azw3 |eng | 2019-12-02 | Author:Blacio, Trinity [Blacio, Trinity]
Chapter Five Olive was furious; her car was totaled, something she sure as hell didn’t need right now, and she hurt like hell. Then, the doctor kept telling her she ...
( Category:
Architecture
January 16,2020 )
azw3, epub |eng | 2015-11-23 | Author:Douglas Boyd
Chapter 18: War on the belly of Dan Dahomey 1892 – 1894 The Legion’s elevation to the status of a brigade in December 1884 made little difference to the units ...
( Category:
Engineering
January 16,2020 )
epub |eng | 2020-01-01 | Author:Howard Axelrod
JUST A FEW SUNDAYS AGO, on Harvard Avenue, I saw a teenager, maybe fifteen or sixteen, who had found her answer. She was with her parents. They were short and ...
( Category:
Essays
January 15,2020 )
azw3, mobi, epub |eng | 2017-04-03 | Author:McRaven, William H. [McRaven, William H.]
CHAPTER SEVEN Stand Up to the Bullie s If you want to change the world… don’t back down from the sharks. T he water off San Clemente Island was choppy ...
( Category:
Leadership
January 15,2020 )
epub |eng | | Author:Cheng-Lin Liu & Fei Liu
Proof The system (3.9) is rewritten as , where . Since the union of n agents’ interconnection topologies across has a spanning tree, is from Lemma 3.3. Because and the ...
( Category:
Engineering
January 15,2020 )
epub |eng | | Author:Subhas Chandra Mukhopadhyay
2.4 TSCH Deterministic Networks The IEEE802.15.4e TSCH, due to the combination of Time Division Multiplexing (TDM), time synchronization and the time formatted into slotframes, results in a deterministic wireless MAC ...
( Category:
Computer Science
January 15,2020 )
epub, pdf |eng | | Author:Joe Larson
Note Try out axis locking with movement, rotation, and scaling, and adjust the view to see what effect it has. Notice that with axis locking, the scale function has some ...
( Category:
Architecture
January 15,2020 )
epub |eng | | Author:Joe Larson
Adjust the view to see how exactly how the object moved. When moved while in the top view, the object stays on the grid plane. This is because from the ...
( Category:
Architecture
January 15,2020 )
epub |eng | | Author:Veronica Hinke
Edith Rosenbaum Russell was outspoken in her contention that the ship’s band did not play “Nearer My God to Thee,” and that it did not continue playing as the Titanic ...
( Category:
Spirits
January 15,2020 )
epub, pdf |eng | | Author:Joe Larson
Select (right-click) the Body and begin to add Boolean modifiers to it. First add a Boolean to Union the Neck to the body. Then add Booleans to Difference the PegLeft, ...
( Category:
Graphics & Design
January 15,2020 )
epub |eng | | Author:Joe Larson
The Boolean modifier is one of the most important tools in Blender that's used to create 3D printable objects. However, it can also be one of the most frustrating to ...
( Category:
Architecture
January 15,2020 )
epub |eng | | Author:Chintan Bhatt, Nilanjan Dey & Amira S. Ashour
Importance of Unsupervised Learning Algorithms in Big data Analytics: Unsupervised learning is one of the most effective way for analyzing big data as no training set data is required here. ...
( Category:
Computer Science
January 14,2020 )
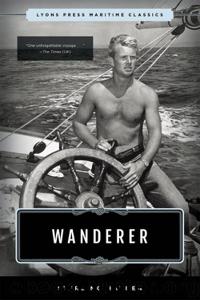
epub |eng | 2019-02-26 | Author:Sterling Hayden
CHAPTER 42 High water. A schooner lies to a wharf. Her sheer is proud as it runs up to her bows from a low point amidships. Old men lounge in ...
( Category:
Boating
January 14,2020 )
epub |eng | | Author:Nik Bessis & Ciprian Dobre
6 Design Decisions and Applications We made a number of design decisions during the development of the CADDOT model. These decisions address the challenges we highlighted in earlier sections. Security ...
( Category:
Computer Science
January 14,2020 )
epub |eng | | Author:Liehuang Zhu, Zijian Zhang & Chang Xu
The privacy-preserving key management(PARK) scheme is proposed in [X]. The privacy-preserving key management scheme uses adaptive key management and revocation to secure customer data from outsiders in the smart grid. ...
( Category:
Networking & Cloud Computing
January 14,2020 )
Categories
| Automotive | Engineering |
| Transportation |
Popular ebooks
Whiskies (Collins Gem) by dominic roskrow(45421)Whiskies Galore by Ian Buxton(42078)
Introduction to Aircraft Design (Cambridge Aerospace Series) by John P. Fielding(33174)
Small Unmanned Fixed-wing Aircraft Design by Andrew J. Keane Andras Sobester James P. Scanlan & András Sóbester & James P. Scanlan(32835)
Aircraft Design of WWII: A Sketchbook by Lockheed Aircraft Corporation(32329)
Craft Beer for the Homebrewer by Michael Agnew(18283)
Turbulence by E. J. Noyes(8110)
The Complete Stick Figure Physics Tutorials by Allen Sarah(7422)
The Institute by Stephen King(7088)
The Thirst by Nesbo Jo(7002)
Kaplan MCAT General Chemistry Review by Kaplan(6985)
Bad Blood by John Carreyrou(6669)
Modelling of Convective Heat and Mass Transfer in Rotating Flows by Igor V. Shevchuk(6492)
Weapons of Math Destruction by Cathy O'Neil(6362)
Learning SQL by Alan Beaulieu(6334)
Man-made Catastrophes and Risk Information Concealment by Dmitry Chernov & Didier Sornette(6137)
Permanent Record by Edward Snowden(5889)
Digital Minimalism by Cal Newport;(5834)
Life 3.0: Being Human in the Age of Artificial Intelligence by Tegmark Max(5616)
iGen by Jean M. Twenge(5452)